Context
As we are all aware of global pandemic due to COVID-19 and its effect on the sudden shift of workforce from office to remote or at home. This sudden shift has given rise to IT and cyber security risks where the employees, consumers or end users using IT system has become vulnerable and one of the weakest chain in the security due to lack of awareness as well as due to usage of less secured authentication mechanism while interacting with IT software/systems which are sensitive or data/information rich in nature vulnerable to data breaches.
Here in this first part of post I will be mainly talking about the awareness on such risks and introduction of MFA (Multi factor authentication) for secure authentication in remote working condition.
Increased risks with this sudden shift
As we have completed more than half of this year (2020) with this pandemic, the security threats posed by it also rage on. The threats and the risk in these times are actually much higher than before the situation including targeted phishing scams, allowing cyber criminals to take advantage of situation when people are in fear, confusion, un-aware and foremost concerned anything related to health.
Here is the emphasized spread of threats during these times based on strength of text:

Out of all the threats, the phishing attacks are the most prominent and highest during these times :

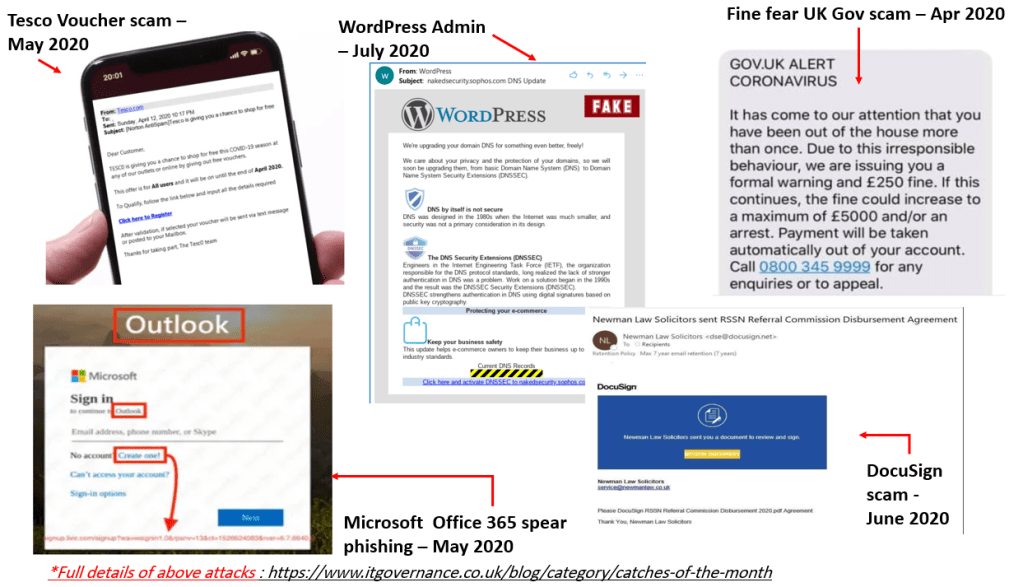
Recent Phishing attacks during COVID-19
Below here are few recent phishing attacks till last month i.e. July 2020. The full details of these attacks can be found in the link mentioned in References section of this post at the end.
How some organizations managing/securing remote working conditions?
Here is a very high level of typical scenarios which most of the organizations fall into when dealing with remote working
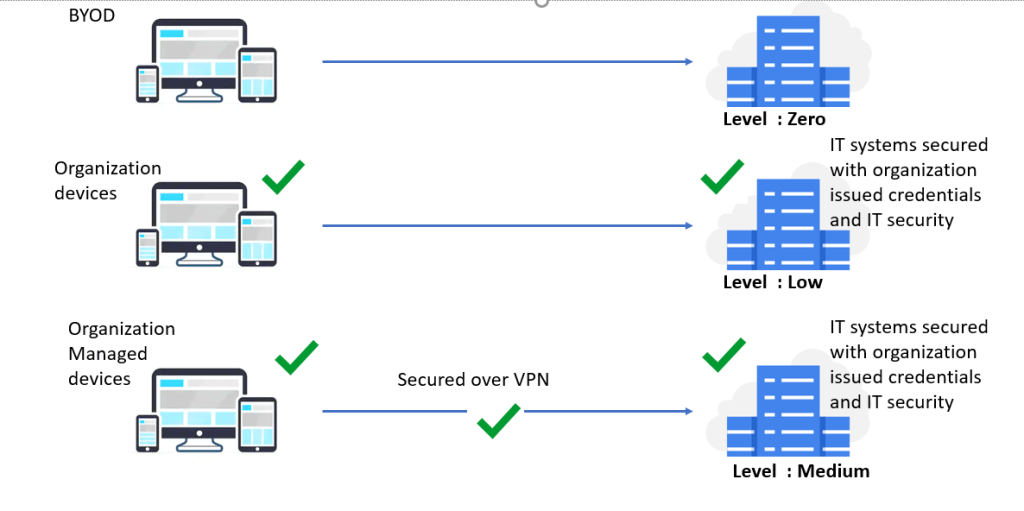
Level zero : The first scenario where the employees using their own devices (laptop, mobile, WiFi router etc.) and are connecting to organization’s IT software/systems with least security and typically secured with username/password.
Level Low: The second scenario where the employees using the devices issued by their organizations with some security policies applied on devices and limited privileges. The access to IT applications/systems is more secured with organization issued credentials and having stricter credential management policies (e.g. password expiry, complexity etc.)
Level Medium: The third scenario where the VPN (Virtual private network) have been enabled for remote workers and the trust is more in terms on secured network. The devices are also fully managed by organization’s security policy.
* These levels are just defined by me for illustrating
In all of the above scenarios the trust is more either towards usage of correct credentials (mainly username/password) and the secured network being in place. Instead, considering the current remote working conditions, the organizations should move towards strong identification and authentication foundations.
Here, I am trying to introduce and leverage the SSO (Single sign on) and MFA (Multi factor authentication) which are less susceptible to inherent to identity theft, phishing, weakness of VPNs etc.
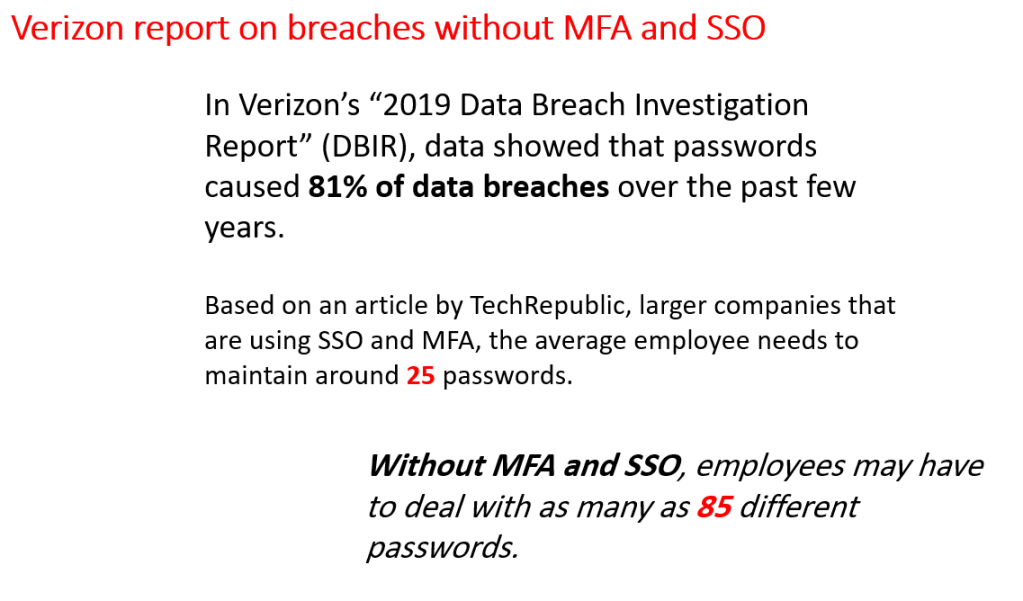
Passwords are not enough and already every body has too many !!
Passwords alone are not enough and we all are aware that they are the weakest link in the chain of cyber security. Employees often either forced to maintain too many passwords and complex password policies or maintain the duplicate passwords making it vulnerable.
So what the heck is MFA and SSO ?
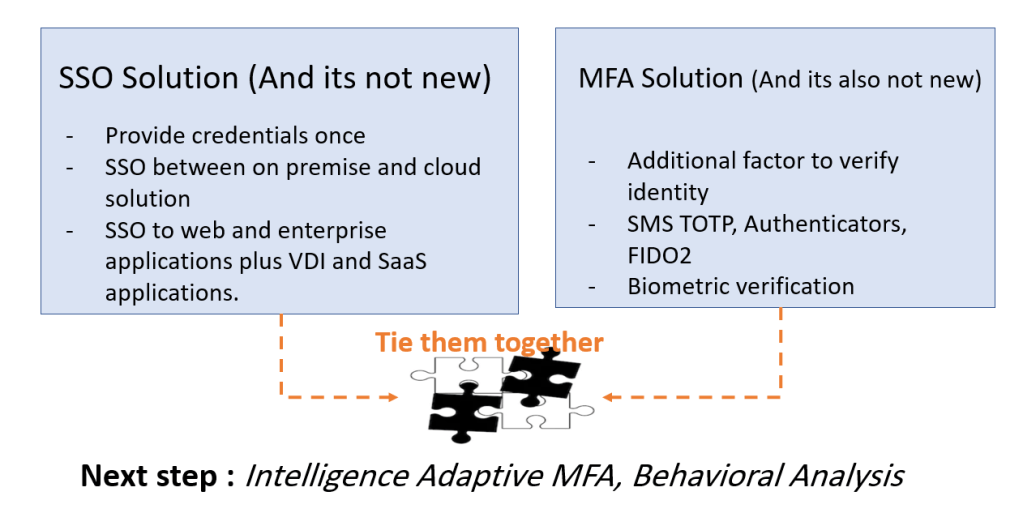
Both MFA (Multi factor authentication) and SSO (Single Sign on) are the not the new concepts at all in IT security space and we are somehow familiar with both while using the IT systems, social networking, bank and financial applications.
You might have experienced MFA when some applications especially banking applications send you an SMS OTP to authenticate or login into their systems
You might have experienced SSO while using Facebook (or Google) where you have logged in to many other sites using Facebook (or Google) login without recreating new password or credentials in those websites or applications.
However, the landscape is changed with rise of new technologies and possession of devices (mobile device and mobile applications) with users to make it more relevant.
- SSO Solutions : The SSO solutions allow users to use their credentials once and can authenticate seamlessly in other SSO enabled application without being re-challenged or challenged with additional factors whenever needed. This eliminates the need of managing multiple credentials. For example : remembering of multiple passwords
- MFA solutions : Multi factor authentication as name suggests relying more than typical passwords to more convenient authentication factors which employees can manage easier than remembering passwords. It can rely on different factors suitable per organization or system/application as below:
- What you know? (Knowledge) – E.g. : username password, security questions etc.)
- What you have? (Possession) – E.g. : Smart card, Smart phones, Hardware tokens etc.)
- What you are? (Biometric) – E.g. : Facial recognition, fingerprint match etc.)
- What we know or learnt? (Behavioral) – E.g. : Deviations from usual patterns, geographical location, usage timings, key stroke patterns etc.)
More details on MFA will be covered in next post
How they gonna solve problems or make things more secure?
Considering all these factors and leveraging easier, more secure factors than passwords actually gives organizations the path or option to move towards “passwordless“.
Being Passwordless is a next stage of maturity in authentication space where the alternative factors can become the primary source or method of authenticating the users. For example, TouchID, Face verification, authenticators app and nonetheless FIDO.
Similarly, leveraging MFA with SSO will give another dimension of security and enhanced user experience where a user can enjoy SSO plus being passwordless at same time and based on various factors and sensitivity of applications in SSO system, the user should be asked for additional factor.
Sample Scenario leveraging MFA and SSO :
A user can login to organization portal using a passwordless mechanism of authentication using the SMS (or email) OTP and can access dashboard to view certain reports. Now user needs to approve a document which is financially sensitive and opens inside another application. Here the SSO will allow user to not provide the first factor of OTP again and will just ask on additional factor e.g. to confirm a push notification sent on the user’s registered device.
Here is the model to club both of them for balancing the trade off between security and user convenience:
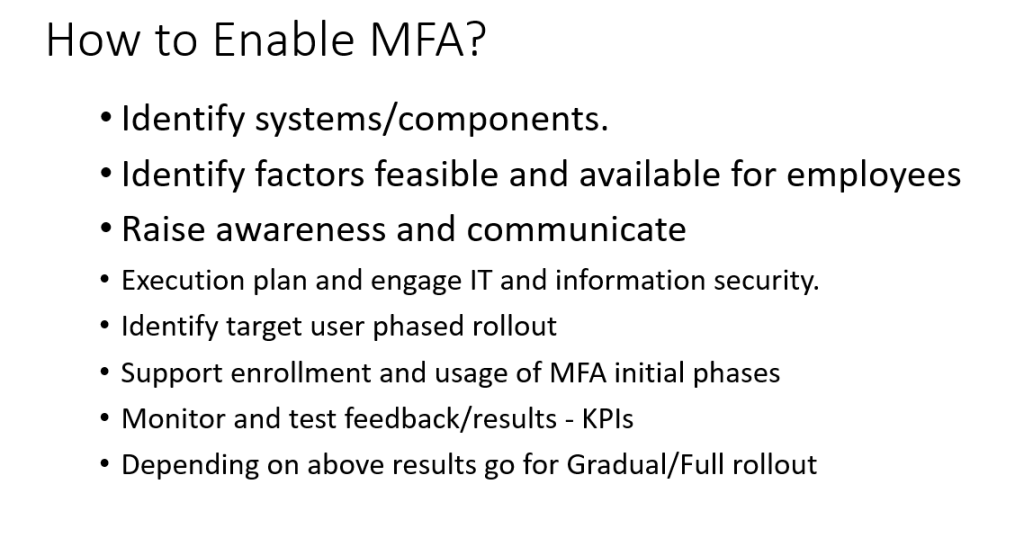
How to enable MFA?
So, I will be talking in more details about enabling MFA in subsequent posts. However, just giving the high level overview on planning about MFA.
At a high level, its just not about the technical enable-ment and rolling out a software, its more about assessing the need and methods applicable for an organization and its employees. At the same time, awareness is the key to combat the recent cyber security threats as highlighted in above sections of the post. Here are few key points to consider:
Lastly, Is MFA vulnerable?
In today cyber security space nothing is 100% secured and as I mentioned earlier also that “awareness is a key“. Its same as COVID-19 situation where we are still sustaining without the vaccination but awareness makes it possible to combat even in absence of it. More the awareness, less the chances of failures and breakdowns.
Having said this, MFA is also not a silver bullet and it may also have vulnerabilites but one can think risks are less than traditional authentication systems. I am jotting down few of them as follows:
References:
- PPTs available in slideshare : https://www.slideshare.net/yusufkhan/secure-authentication-in-the-age-of-remote-working-and-covid19-mfa
- Phishing scam details mentioned in this post : https://www.itgovernance.co.uk/blog/category/catches-of-the-month
- Verizon’s “2019 Data Breach Investigation Report” (DBIR),
- Barracuda Networks
Disclaimer : All the views and opinion expressed in this website or blog are personal and belong solely to the author and does not represent any organization, institution, employer that the author may or may not be associated with in a professional or personal capacity.